TL;DR
- Analysts investigating the cause of the Drift Protocol hack linked the exploit to North Korean-affiliated groups.
- Early analysis suggests similarities to the 2025 Bybit breach, including potential multisig or privileged access compromise.
- Attribution and exact exploit mechanics remain unconfirmed pending a full postmortem from Drift.
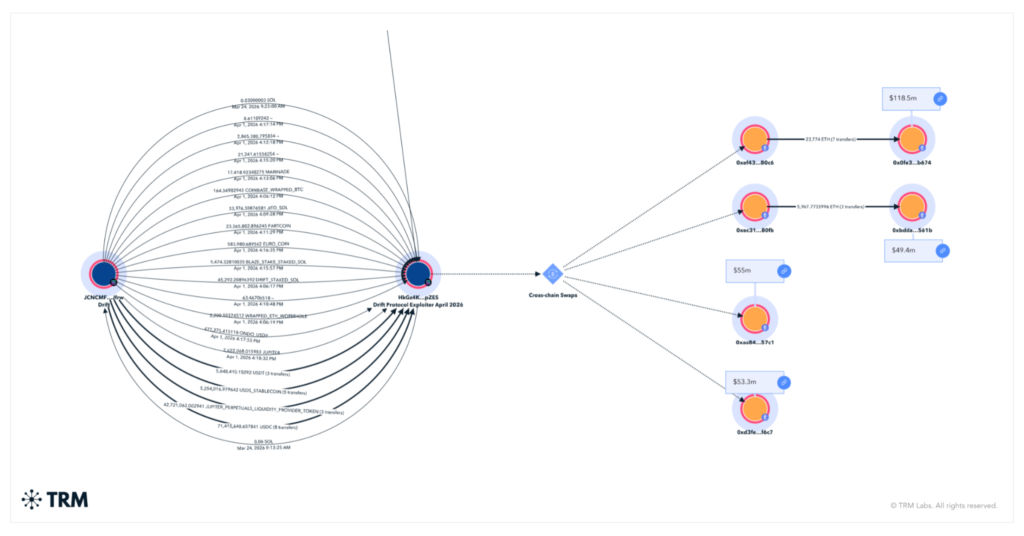
The investigation into the causes of the Drift Protocol hack has shifted toward attribution and attack structure. Blockchain analytics firms, including TRM Labs and Elliptic, have linked the exploit to North Korean-affiliated hacking groups. The incident saw hundreds of millions drained from the Solana-based platform. It is now being analyzed not just as an isolated breach but as part of a broader pattern of state-linked crypto attacks.
Drift has not yet released a full technical breakdown. External investigators point to coordinated behavior consistent with previous high-profile exploits. These include rapid fund movement, cross-chain transfers, and structured laundering patterns often associated with advanced threat actors.
North Korea link gains traction among analysts
Cybersecurity analysis from TRM Labs and Elliptic suggests the attackers may be tied to North Korean groups. These groups are known for targeting crypto platforms. They have been linked to multiple large-scale hacks in recent years. Their activity often focuses on DeFi protocols and centralized exchanges.
The attribution is based on transaction patterns, wallet clustering, and behavioral similarities observed in prior incidents. However, this assessment remains probabilistic. Drift has not officially confirmed responsibility at this stage.
For readers, this distinction matters. Attribution in crypto exploits often relies on forensic analysis rather than direct identification. Conclusions can evolve as more data becomes available.
Parallels to last year’s Bybit hack
Analysts are examining the cause of the Drift Protocol hack by comparing it to the 2025 Bybit breach. That incident involved a significant compromise of internal controls. Security researchers and industry executives have pointed to structural similarities between the two incidents. This includes commentary cited by TRM Labs and other analysts.
One recurring theory is the use of a multisig or privileged access vulnerability. In this scenario, attackers gain control over critical administrative functions. They do not rely on a simple smart contract bug — the attack surface shifts from code-level flaws to operational security weaknesses.
The comparison is notable. The Bybit hack showed how attackers could bypass standard safeguards. They did this by targeting governance or signing mechanisms. Early analysis suggests Drift may have faced a similar vector. This has not been officially confirmed.
Attack execution suggests prolonged preparation
Further analysis from TRM Labs indicates the exploit may not have been opportunistic. It may have been carefully staged. Investigators suggest the attackers could have spent weeks positioning themselves within the system. The drain itself was then executed in a short time window.
This pattern aligns with previous large-scale crypto breaches. Attackers establish access gradually. They test system responses. They then execute the main exploit rapidly to minimize detection and intervention.
If confirmed, this would reinforce the view that the Drift incident was not simply a technical failure. It may reflect a broader security breakdown involving monitoring, access controls, or internal safeguards.
Industry implications extend beyond Drift
The Drift Protocol hack is likely to have wider implications, particularly as its cause raises concerns about how crypto platforms approach security. This is especially true for privileged access and cross-chain infrastructure. The incident has already prompted renewed discussion about multisig protections, real-time monitoring, and response coordination across ecosystems.
It also raises questions about the limits of existing defenses against well-resourced attackers. Even when vulnerabilities are not visible at the smart contract level, operational weaknesses can still expose large pools of capital.
Until Drift releases a detailed postmortem, much of the analysis will remain provisional. However, the emerging picture, supported by firms such as Elliptic and TRM Labs, points to a sophisticated attack. It may share characteristics with previous state-linked exploits rather than a simple isolated failure.